When you connect multiple devices to a network switch, the switch normally forwards broadcasts and multicasts to every port (except the one that sent the traffic). This means all devices can “hear” each other, which can create unnecessary noise and reduce performance in large networks.
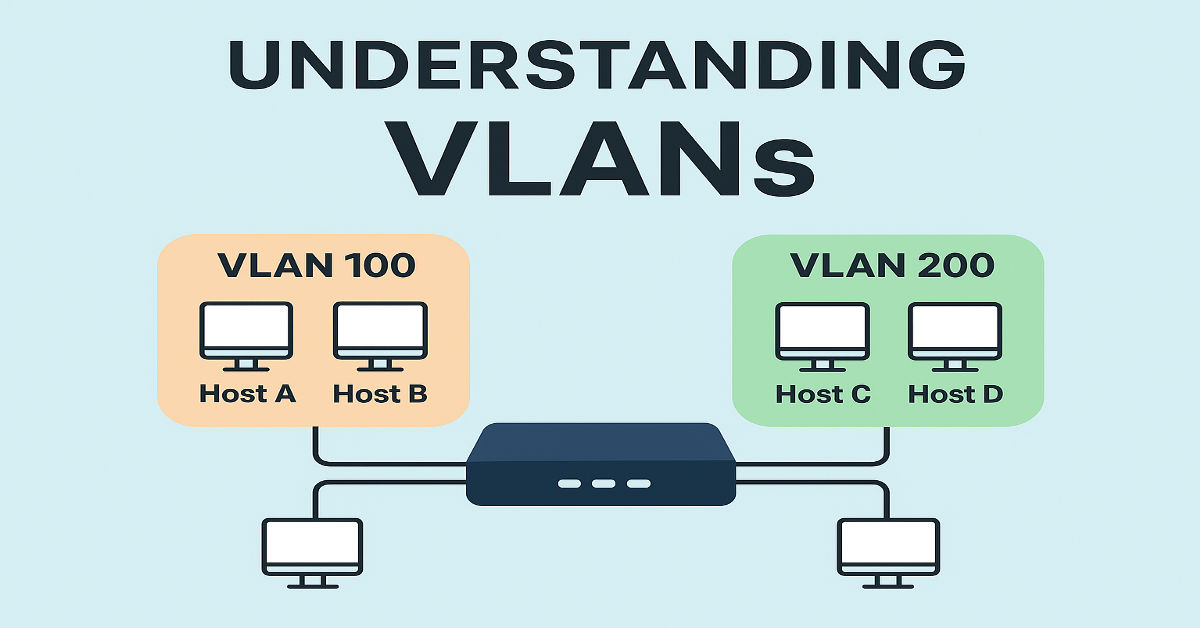
That’s where VLANs (Virtual Local Area Networks) come in. VLANs allow us to logically break a switch into separate sections, so each section behaves like an independent network — even though they all run on the same physical switch.
Think of VLANs as “virtual walls” inside your switch that separate traffic, improve performance, and increase security.
What is a VLAN?
A VLAN is a logical broadcast domain created on a switch. Devices inside the same VLAN can directly communicate with each other. But if devices are in different VLANs, they cannot talk without the help of a Layer-3 device (like a router or Layer-3 switch).
- Traffic within a VLAN is switched at Layer 2 (Data Link Layer).
- Traffic between different VLANs needs a Layer 3 device to route the packets.
- VLAN tagging happens in the Layer 2 Ethernet header, which means VLANs are not a Layer 3 feature, even though they separate broadcast domains.
Quick Reminder: A VLAN often corresponds to an IP subnet (like VLAN 10 = subnet 192.168.10.0/24), but this is not a strict requirement.
VLAN Example
Imagine a switch with four devices connected:
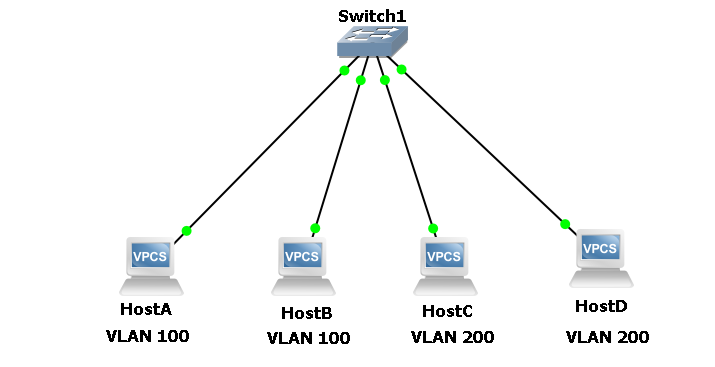
- Host A and Host B → VLAN 100
- Host C and Host D → VLAN 200
Here’s what happens:
- Host A can talk to Host B (same VLAN, same broadcast domain).
- Host C can talk to Host D (same VLAN, same broadcast domain).
- But Host A/B cannot talk directly to Host C/D (different VLANs, different broadcast domains).
If communication is needed between VLAN 100 and VLAN 200, a router or Layer-3 switch must be used.
Also, if Host A sends a broadcast, only devices in VLAN 100 will receive it. Devices in VLAN 200 will never see that traffic.
On Cisco switches, all ports are in VLAN 1 by default, which is also the Management VLAN used for system-level traffic (like CDP, STP, VTP, and DTP).
Why Do We Use VLANs?
VLANs aren’t just about separation; they bring some real benefits:
- Broadcast Control
- Reduce unnecessary traffic by keeping broadcasts within a VLAN.
- This improves performance and scalability.
- Better Security
- Devices in one VLAN cannot access devices in another VLAN unless explicitly allowed through routing/firewall rules.
- Helps isolate departments (e.g., HR vs. Finance).
- Flexibility & Efficiency
- Users can be placed in the same VLAN no matter where they physically connect.
- Makes network management simpler.
Common usage: separating user VLANs from server VLANs in an office or campus network.
VLAN Membership Types
There are two main ways devices get assigned to a VLAN:
- Static VLANs (Most Common)
- Manually assign a switch port to a VLAN.
- Any device plugged into that port automatically becomes part of that VLAN.
- Example:
| Switch(config)# interface gi1/10 Switch(config-if)# switchport mode access Switch(config-if)# switchport access vlan 100 |
- Dynamic VLANs
- VLAN membership is assigned based on the device’s MAC address.
- Even if you move the device to another switch port, it stays in the same VLAN.
- Requires a VLAN Membership Policy Server (VMPS).
- More advanced systems may assign VLANs based on a user’s login credentials.
Creating VLANs on a Cisco Switch
By default, all ports are part of VLAN 1. To create a new VLAN:
| Switch(config)# vlan 100 Switch(config-vlan)# name SERVERS |
- VLAN 100 is created.
- It’s given the name “SERVERS” (naming is optional).
VLAN ranges:
- Normal VLANs: 1–1005 (1002–1005 reserved for old technologies).
- Extended VLANs: 1006–4094 (only available in VTP transparent mode).
To delete a VLAN:
| Switch(config)# no vlan 100 |
VLAN Database & Persistence
- On switches in VTP server/client mode, VLANs are stored in a file called vlan.dat (usually in flash).
- On switches in VTP transparent mode, VLANs are stored in the startup-config (NVRAM).
- VLAN assignments for each interface are saved in the switch’s configuration.
This means VLANs and their port mappings survive reboots.
Wrapping It Up
VLANs are one of the most powerful tools in modern networking. They give us:
- Better performance by controlling broadcasts
- Stronger security by isolating traffic
- Flexible network design without physical restrictions
Without VLANs, large networks would quickly become chaotic, insecure, and hard to manage.